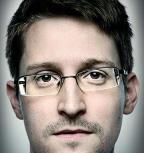
DLP: The evolution of Data Loss Prevention
This time-line of high profile data leaks
shows the evolution in methods, technologies and types of data leaked.
The main targets are healthcare, client information, trade secrets, plans, designs and strategies.
Data Loss Prevention improvements have tended to be fairly reactive to this .. so far. But as in the Morrisons example
companies are now being held liable for rogue insider data leaks.
1820: Early Industrial Espionage
 Information was valuable way before computers.
In the 19th century as Britain emerged as an "industrial creditor", France sponsored a large-scale effort to surreptitiously
take British industrial technology, particularly coal, metalworking-based technologies, to France.
The French placed apprentices in key British positions and lured or corrupted skilled British tradespeople.
Information was valuable way before computers.
In the 19th century as Britain emerged as an "industrial creditor", France sponsored a large-scale effort to surreptitiously
take British industrial technology, particularly coal, metalworking-based technologies, to France.
The French placed apprentices in key British positions and lured or corrupted skilled British tradespeople.
Harris, John (1998). Industrial Espionage and Technology Transfer: Britain and France in the Eighteenth Century
Details
- Insider: Corrupted British tradespeople; Supplanted French apprentices
- Target: Britain
- Industry: Industry (esp Coal)
- Date: 1820's
- IP Stolen: Industrial Techniques
- Method Of Theft: Placing & influencing insiders
1973-2006: Space Shuttle Designs
 Dongfan “Greg” Chung of California was employed by Rockwell International from 1973 until its defense and space unit was acquired by Boeing in 1996.
He held a “secret” security clearance when he worked at Rockwell and Boeing on the Space Shuttle program.
Chung retired from the company in 2002, but the next year he returned to Boeing as a contractor, a position he held until September 2006.
During the trial, the government proved that Chung stole Boeing trade secrets relating to the Space Shuttle, the Delta IV rocket
and various military and civilian aircraft; materials he acquired for the benefit of the PRC.
Dongfan “Greg” Chung of California was employed by Rockwell International from 1973 until its defense and space unit was acquired by Boeing in 1996.
He held a “secret” security clearance when he worked at Rockwell and Boeing on the Space Shuttle program.
Chung retired from the company in 2002, but the next year he returned to Boeing as a contractor, a position he held until September 2006.
During the trial, the government proved that Chung stole Boeing trade secrets relating to the Space Shuttle, the Delta IV rocket
and various military and civilian aircraft; materials he acquired for the benefit of the PRC.
Details
- Insider: Dongfan “Greg” Chung
- Target: Boeing, Rockwell and other defence contractors
- Industry: Aerospace
- Date: 1973 - 2006
- IP Stolen: Space shuttle designs, stress analysis reports, test results and aircraft design manuals
- Method Of Theft: Paper documents & manuals: 250,000+ pages
1993: $100m Car maker Industrial Espionage
 In 1993, Opel, the German division of General Motors, accused Volkswagen of industrial espionage after Opel's chief of production,
Jose Ignacio Lopez, and seven other executives moved to Volkswagen.
Lopez specialised in managing the purchases of car components from suppliers.
He had significantly reduced GMs purchasing costs from suppliers in the early 1990s before taking a similar role as VW.
GM said Lopez took with him 20 boxes full of confidential data on the company's future-product plans and pricing information
on 60,000 auto components.
In 1993, Opel, the German division of General Motors, accused Volkswagen of industrial espionage after Opel's chief of production,
Jose Ignacio Lopez, and seven other executives moved to Volkswagen.
Lopez specialised in managing the purchases of car components from suppliers.
He had significantly reduced GMs purchasing costs from suppliers in the early 1990s before taking a similar role as VW.
GM said Lopez took with him 20 boxes full of confidential data on the company's future-product plans and pricing information
on 60,000 auto components.
Volkswagen threatened to sue for defamation, resulting in a four-year legal battle.
The case was finally settled in 1997 with one of the largest payouts in the history of industrial espionage.
Details
- Insider: Jose Ignacio Lopez & 7 other executives
- Target: GM (Opel)
- Industry: Car Manufacturing
- Date: 1993
- IP Stolen: Purchasing / supply chain trade secrets
- Method Of Theft: Boxes of Paper documents: "thousands of pages of company documents"
2009: T-Mobile Customer Data Stolen & Sold
 Personal details of thousands of T-Mobile mobile phone customers have been stolen and sold to rival firms in the biggest data breach of its kind.
The millions of items of information were sold on for "substantial sums", the Information Commissioner's Office (ICO) said.
The commissioner's office is pushing for stronger powers to halt the unlawful trade in personal data, which is growing due to cut-throat competition among mobile phone companies.
"The number of records involved runs into the millions, and it appears that substantial amounts of money changed hands," the ICO said
Personal details of thousands of T-Mobile mobile phone customers have been stolen and sold to rival firms in the biggest data breach of its kind.
The millions of items of information were sold on for "substantial sums", the Information Commissioner's Office (ICO) said.
The commissioner's office is pushing for stronger powers to halt the unlawful trade in personal data, which is growing due to cut-throat competition among mobile phone companies.
"The number of records involved runs into the millions, and it appears that substantial amounts of money changed hands," the ICO said
Details
- Insider: David Turley, Darren Hames
- Target: T-Mobile
- Industry: Mobile Telecoms
- Date: 2009
- IP Stolen: Customer Data,
specifically renewal details - Method Of Theft: USB Stick
2009: Stolen Trading Software Leads To Troublesome Legal Battle
 Goldman Sachs programmer Sergey Aleynikov took proprietary trading source-code from his then employer
days before leaving his job.
Aleynikov encrypted files from Goldman Sachs's network and transferred them to a website hosted in Germany.
He covered his tracks by erasing the encryption program and attempting to delete the command history showing his activity,
according to court records.
Goldman Sachs programmer Sergey Aleynikov took proprietary trading source-code from his then employer
days before leaving his job.
Aleynikov encrypted files from Goldman Sachs's network and transferred them to a website hosted in Germany.
He covered his tracks by erasing the encryption program and attempting to delete the command history showing his activity,
according to court records.
Assistant US attorney Joseph Facciponti called it “the most substantial theft that the bank can remember ever happening to it,”
and said the theft constituted the company’s “entire platform” for high-speed trading.
Despite Goldman Sachs' determination and might, the legal battle proved a difficult and expensive way to address the issue.
From Aleynikov's first conviction in 2011 a number of appeals and twists have involved different federal & state laws
under which to try Aleynikov.
Details
- Insider: Sergey Aleynikov
- Target: Goldman Sachs
- Industry: Investment Banking
- Date: 2009
- IP Stolen: Computer Software;
32Mb to 1,224Mb code (amount disputed) - Method Of Theft: Upload to the internet
2010: Manning & the Lady Gaga CD
 While working as an Army Intelligence Analyst at Forward Operating Base Hammer (40 miles east of Baghdad, Iraq)
Bradley Manning held a Top Secret/SCI clearance giving him access to classified information.
Manning downloaded classified videos of military operations in Iraq
and abused access to the Secret-level SIPR network to obtain more than 150,000 U.S. State Department cables.
While working as an Army Intelligence Analyst at Forward Operating Base Hammer (40 miles east of Baghdad, Iraq)
Bradley Manning held a Top Secret/SCI clearance giving him access to classified information.
Manning downloaded classified videos of military operations in Iraq
and abused access to the Secret-level SIPR network to obtain more than 150,000 U.S. State Department cables.
Manning had access to two classified networks from two separate secured laptops: SIPRNET, used
by the Department of Defence and the State Department, and the Joint Worldwide Intelligence Communications System which
serves both agencies at the Top Secret/SCI level.
The networks, Manning said, were both “air gapped” from unclassified networks, but the environment at the base made it easy to
smuggle data out. “I would come in with music on a CD-RW labelled with something like ‘Lady Gaga’ erase the music then write a compressed split file”
Details
- Insider: Bradley Manning
- Target: US Army
- Industry: Armed Forces / Government Intelligence Agency
- Date: 2010
- IP Stolen: Thousands of classified documents & videos
150,000 to 400,000 documents (amount disputed) - Method Of Theft: CD-RW
2011: Hedge Fund alpha's & computer code
 Yihao "Ben" Pu was a quantitative engineer at the Chicago based hedge fund Citadel, working on High-Frequency Trading.
Citadel is among the worlds most successful computerised trading based hedge funds.
Pu was arrested and later sentenced for stealing sensitive
information about the fund's computer-driven trading strategies, downloading it to personal hard drives
other electronic storage devices - Citadel already blocked USB ports on their computers.
Pu attempted to destroy the devices in a canal but they were recovered by divers and found to contain Citadel material.
Yihao "Ben" Pu was a quantitative engineer at the Chicago based hedge fund Citadel, working on High-Frequency Trading.
Citadel is among the worlds most successful computerised trading based hedge funds.
Pu was arrested and later sentenced for stealing sensitive
information about the fund's computer-driven trading strategies, downloading it to personal hard drives
other electronic storage devices - Citadel already blocked USB ports on their computers.
Pu attempted to destroy the devices in a canal but they were recovered by divers and found to contain Citadel material.
"We obviously pay a lot of attention to protecting our intellectual property," said Citadel boss Ken Griffin,
adding that it was incredibly important for him to protect his fund's computer code. "You know all this is, is idea, thoughts,
and concepts expressed in computer code. And unfortunately that intellectual property is readily moved, and it's very important
for us to protect it,"
Pu also confessed to previously taking computer code from his former employer, Tradeworx, a New Jersey based firm.
He was sentenced to three years in prison.
Details
- Insider: Yihao Ben Pu
- Target: Citadel
- Industry: Hedge Fund
- Date: 2011
- IP Stolen: Trading Computer Code
- Method Of Theft: Personal External Hard-Drive
2013: Snowden & the USB Thumb Drive
 Edward Snowden was a contractor from Booz Allan Hamilton working as a systems administrator at the NSA in Hawaii.
He asked for a leave of absence, then absconded with documents he'd taken from the NSA network using a USB thumb drive
and flew to Hong Kong.
Edward Snowden was a contractor from Booz Allan Hamilton working as a systems administrator at the NSA in Hawaii.
He asked for a leave of absence, then absconded with documents he'd taken from the NSA network using a USB thumb drive
and flew to Hong Kong.
Thumb drives were already recognised as a threat.
In 2010 Maj. Gen. Richard Webber, commander of Air Force Network Operations, sent out a notice
to “immediately cease use of removable media on all systems, servers, and stand alone machines residing on SIPRNET,”
the Defense Department’s secret network.
“Unauthorized data transfers routinely occur on classified networks using removable media and are a method the insider threat
uses to exploit classified information," the note said. "To mitigate the activity, all Air Force organizations must immediately
suspend all SIPRNET data transfer activities on removable media." Similar notices went out to other branches of the military.
However administrators of these systems use thumb drives for tasks like applying updates to standalone "Air-Gapped" systems not
connected to the main network. As a system administrator Snowden had more freedom and access on the NSA's networks than average workers.
He also likely would have drawn little suspicion with a thumb drive.
The total cost of Snowden's data breach has been estimated at around $35bn.
Details
- Insider: Edward Snowden
- Target: NSA
- Industry: Government Intelligence Agency
- Date: 2013
- IP Stolen: Thousands of classified documents
- Method Of Theft: USB Thumb Drive
2013: Swiss Bank Client Data
 In 2013 Credit Suisse sued a former vice president of its emerging markets group,
claiming she stole confidential documents and trade secrets to transfer business to her new employer, Goldman Sachs.
In 2013 Credit Suisse sued a former vice president of its emerging markets group,
claiming she stole confidential documents and trade secrets to transfer business to her new employer, Goldman Sachs.
Credit Suisse said Agostina Pechi sent confidential and highly sensitive company documents to her personal email account
in the months leading up to her resignation, including databases, deal-structuring documents, client contact information
and sales team targets.
They also accused Pechi of printing documents after-hours when she was scheduled to be on vacation.
Details
- Insider: Agostina Pechi
- Target: Credit Suisse
- Industry: Banking
- Date: 2013
- IP Stolen: Client & Sales data
- Method Of Theft: Email & Printing
2014: Morrisons liable for payroll data breach
 At the hearing of the UK’s first data leak class action, the supermarket chain, Morrisons, has been found liable for the information breach caused by former employee, Andrew Skelton, back in 2014.
At the hearing of the UK’s first data leak class action, the supermarket chain, Morrisons, has been found liable for the information breach caused by former employee, Andrew Skelton, back in 2014.
5,000 employees brought a claim against Morrisons after Skelton, a former auditor for Morrisons, stole their sensitive data, such as names, addresses, salary and bank details, posted the information on-line, and sent on a disc to newspapers over a “personal grievance” against the company.
His motive appeared to have been a grudge over a previous incident when he was accused of dealing in legal highs at work. Skelton was jailed for eight years in 2015.
"The High Court has ruled that Morrisons was legally responsible for the data leak. We welcome the judgement and believe that it is a landmark decision, being the first data leak class action in the UK," Nick McAleenan of JMW Solicitors said of the ruling.
Details
- Insider: Andrew Skelton
- Target: Morrisons
- Industry: Retail / Supermarket
- Date: 2016
- IP Stolen: Pay and bank account details of about 100,000 staff
- Method Of Theft: Disc & uploaded to data sharing websites
2016-2017: Waymo & Uber - Tech giants trade secrets
 Waymo sued Uber in February 2017, claiming that former engineer Anthony Levandowski downloaded more than 14,000 confidential
files before leaving to set up a self-driving truck company, called Otto, which Uber acquired shortly afterwards.
The claims centre on Lidar, a key sensor technology for self-driving cars.
Waymo claims that Otto is using Lidar sensors that bear a striking resemblance to those of its own and that Levandowski
misappropriated a crucial and highly confidential piece of intellectual property owned by the company (for example using a
single lens rather than one for sending and one for receiving).
Waymo sued Uber in February 2017, claiming that former engineer Anthony Levandowski downloaded more than 14,000 confidential
files before leaving to set up a self-driving truck company, called Otto, which Uber acquired shortly afterwards.
The claims centre on Lidar, a key sensor technology for self-driving cars.
Waymo claims that Otto is using Lidar sensors that bear a striking resemblance to those of its own and that Levandowski
misappropriated a crucial and highly confidential piece of intellectual property owned by the company (for example using a
single lens rather than one for sending and one for receiving).
Uber have since fired Levandowski, who is remaining quiet. In February 2018 Uber settled for $245m.
Details
- Insider: Anthony Levandowski
- Target: Google parent Alphabet (Waymo)
- Industry: Tech / Self Driving Cars
- Date: 2016-2017
- IP Stolen: LIDAR designs & trade secrets
9.7 gigabytes (allegedly) - Method Of Theft: External Hard-Drive
2016: Anthem Healthcare
 Anthem's was still reeling from their 2015 hack and data breach when an employee of insurance coordination sub-contractor LaunchPoint Ventures
emailed 18,500 Anthem Medicare member records to their private email account.
The employee was "likely involved in identity theft related activities" and had also misused another LaunchPoint client's data.
Anthem's was still reeling from their 2015 hack and data breach when an employee of insurance coordination sub-contractor LaunchPoint Ventures
emailed 18,500 Anthem Medicare member records to their private email account.
The employee was "likely involved in identity theft related activities" and had also misused another LaunchPoint client's data.
The personal information on the file primarily included Medicare ID numbers (HICN) which includes a Social Security number, Health Plan ID numbers (HCID), Medicare contract numbers, and dates of enrolment. Some last names and dates of birth were also included.
Details
- Insider: Sub-contractor (LaunchPoint) Employee
- Target: Anthem
- Industry: Healthcare
- Date: 2016
- IP Stolen: 18500 Medicare members data
- Method Of Theft: Email
2017: Bupa Healthcare
 A Bupa employee inappropriately copied and removed information relating to 547,000 international health insurance plan customers including
names, dates of birth, nationalities, some contact and administrative information.
"Despite many of us being trustworthy, there are some insiders that break and damage that trust." said Paul Edon at security software firm Tripwire.
A Bupa employee inappropriately copied and removed information relating to 547,000 international health insurance plan customers including
names, dates of birth, nationalities, some contact and administrative information.
"Despite many of us being trustworthy, there are some insiders that break and damage that trust." said Paul Edon at security software firm Tripwire.
According to The Register: "USB ports arguably ought to be disabled at a health insurance provider but that still leaves the possibility of more stealthy data extraction methods. DLP tech is thus far limited to prevent accidental data leaks and unimaginative data thieves only."
Details
- Insider: Bupa Employee
- Target: Bupa
- Industry: Healthcare
- Date: 2017
- IP Stolen: Insurance customer data
- Method Of Theft: Undisclosed copying

