Security Analytics
Identify Rogue Insiders ... ASAP
BM’s 2016 Cyber Security Index, stated that 60% of the year’s breaches were caused by an insider threat.
Whether an enterprise faces a sophisticated Advanced Persistent Threat (APT) or insider threat, indications of breaches can be gathered by analysing data.
The collection and aggregation of data has never been more crucial.
Our platform examines network flows such as DNS, to learn, identify, classify and report suspicious behaviour that can be associated with cyber attack techniques.
Machine learning and security analytics quickly identify cyber threats.
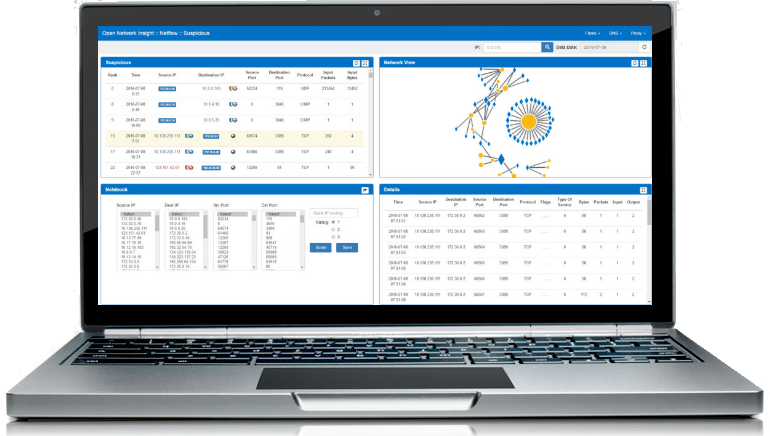
We give organisations the ability to conduct real-time analysis of machine-generated data and user behaviour in key applications to identify anything unusual for further investigation.
Responding to an anomaly quickly shows an organisation’s competence to both identify and deal with cyber-threats.
It can also prove a constructive process for improving cyber threat awareness, as well as building trust in your organisation.
- Most insider events were triggered by a negative event in the workplace.
- Most perpetrators had prior disciplinary issues.
- Most insider events were planned in advance.
- Only 17 percent of the insider events studied involved individuals with root access.
- 87 percent of the attacks used very simple user commands that didn't require any advanced knowledge.
- 30 percent of the incidents took place at the insider's home using remote access to the organization's network.

